New on CGO
SIP & SAVOR SPRING, PRESENTED BY CALLAWAY RESORT & GARDENS
Sip & Savor Spring, Presented by Callaway Resort & Gardens Final Schedule and New James Beard Foundation DInner Chefs Announced March 5, 2018—PINE MOUNTAIN, GA. Sip & Savor Spring is the new culinary celebration, March [continue reading]
Latest Posts
SIP & SAVOR SPRING, PRESENTED BY CALLAWAY RESORT & GARDENS
Callaway Resort & Gardens, Sip & Savor Spring March 15–18, 2018
Historic Fox Theater – Atlanta Georgia, Still going Strong
Halloween Memory from Matthew Reilly
A Patriot in “The Patriot” movie – new story by Matthew Reilly
15 Contractor Questions to make sure you get what you paid for?
Knick-Knacks
4 Ways to Keep Seniors Weather-Safe in Georgia Year Round
by Guest Author in CGO News 0
Civil War in Columbus, Ga.
-
Civil War Civil War Columbus Ga – Part 1
November 30, 2012 0The last land battle of the Civil War was fought in Columbus. Northern troupes marched down Summerville Rd. after dark, but were engaged at the 14th St. bridge. [continue reading]
-
Blow to the Heart of Dixie, Civil War part 2
November 30, 2012 0 -
Civil War – Battle for the Heartland, by Ron Rollins – part 3
November 30, 2012 0 -
Civil War – Surgery to the Heart of Dixie – part 4
November 30, 2012 0 -
Civil War – Last Battle Columbus, Ga – part 5
November 30, 2012 0
News DIgest
TRUMP The Hammer and the Nail
The Hammer and the Nail. A “citizen president” is what this nation has needed for a long time. Lawyers have dominated politics, and I’m tired of it. [continue reading]
Democracy is broken all over Europ
Europe’s democracies are looking dangerously dysfunctional — and some of them are verging on despotic. [continue reading]
Historic Fox Theater – Atlanta Georgia, Still going Strong
My wife and I went to the Fox Theater in Atlanta to see Buster Keaton in “The General.” My wife had never been to the Fox and I told her that she was in for a treat. [continue reading]
Of interest
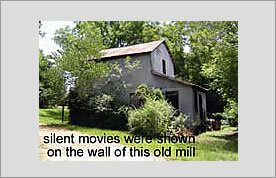
Kodacolor Dreams chap 1
My earliest memories are of a kodacolor dream world. Darkness surrounds a fading white rectangle. For the next ninety minutes a celluloid photo play, shrouded in darkness, would dance on that white rectangle. [continue reading]
Whitesville Picture Show
J. T. placed two large white sheets on the wall of the Mill which was 40ft east of the Cox Store to show the movie on. [continue reading]
Horace King Bridge Builder
Who was Horace King? As a young boy, I was raised in Phenix City, Alabama;on Ingersole Hill over looking the Phenix Drive In Theater and the Hitching Post Drive In cafe. I was like most [continue reading]
Houston Sports Hosital tips
Sciatica
Because sciatica is often caused by irritation, a brief period of rest and avoiding certain activities while taking anti-inflammatory medication is recommended. [continue reading]
Compartment syndrome
Compartment syndrome is a condition in which the pressure in the soft tissues of a limb is abnormally high, resulting in diminished blood flow to the affected extremity. [continue reading]
What is MRSA?
Methicillin-resistant Staphylococcus aureus also known as MRSA, is caused by staphylococcus aureus bacteria (staph). [continue reading]
CT Scan
CT Scans or CAT scans photographs our inside then a computer processes the information and shows a cross-section of body tissues and organs. [continue reading]
What is Osgood-Schlatters Disease
Osgood-schlatters disease is a condition where the boney protrusion just below the knee also known as the tibial tubercle becomes painfully enlarged. As the quadriceps tendon passes over the knee cap it attaches to the tibial tubercle. [continue reading]